A one-time use credit card is a credit card number that can be used once and only for a limited time. It’s commonly used as an alternative to traditional credit cards when making online payments, especially when shopping online. It provides better financial security and privacy for users. A select number of banks offer this […]
Online Security Tips
Welcome to some of the best personal online security tips you'll find anywhere on the web!
Scroll through our most recent articles here or you can follow our step-by-step cybersecurity start page. My hope is that you'll be able to use these cybersecurity tips to lock down your online accounts, create better passwords, and browse the internet more securely.
You don't have to be tech-savvy and you don't have to spend a lot of money. These tips from All Things Secured can be done in just a few minutes or less and can make a drastic difference in your overall security and privacy online.
So what are you waiting for?!
Start browsing these online security tips NOW!
⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓⇓
4 Best Password Strength Checkers in 2026 (& how to use them)
Password strength checkers are becoming quite popular as the fight for more secure online logins gets more attention. There are some good ones (and a lot of bad password checkers) out there, but most people don’t use them correctly. If password security is a priority for you, you’ll want to bookmark these top 4 best […]
Should You Still Use Zoom in 2026? Security Recommendation
Perhaps you remember the news about Zoom’s security issues a while back but maybe you don’t care. Maybe you’re satisfied that they fixed the issues or maybe you only use Zoom for personal group calls where nothing top-secret is shared. You don’t have to stop using it, right? In some cases you might not have […]
What is a Double Blind Password? Password Manager Hack 2026
Double blind password refers to a secure way to store passwords within a password manager app that keeps the real password hidden from both the app and the user. This method is a recommended solution for those who want the convenience of a password manager app without the potential risks of a security breach. The following […]
7 Free Online Security Tools for 2026 You NEED to Use NOW!
Despite all the marketing we’re being fed, protecting your online privacy and digital security doesn’t have to cost you hundreds of dollars a month. These 7 free online security tools are what I recommend to protect you from online identity theft and hacking. I’ve said this before, but it’s worth saying this over and over […]
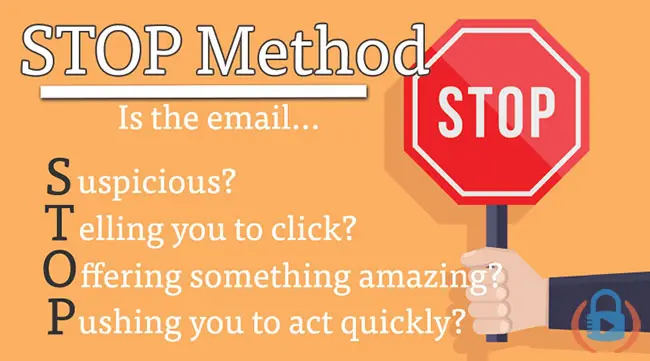
Defeat Email Phishing Scams in 2026 Using the STOP Method
Email phishing scams are often the biggest threats to our personal online security. And yet most of the time we ignore them because we think we’re too smart to fall for them. Watch out! The best way to defeat email phishing scams is to be alert and prepared…but how do you do that? Using the […]