Without even thinking about it, we type SO MUCH personal information into this tiny little rectangle known as a search bar. But what if there were a way to search anonymously? In this tutorial, we’re going to explore some free and simple ways to do more private searches online. There are so many different reasons […]
5 Best Data Broker Removal Services 2026
202The internet has become a catalog of the world’s data, which includes your personal information. Data brokers, people finders and online databases now scrape, buy and sell your data without your knowledge or consent – but you can fight back. Data deletion services can work on your behalf to erase this information off of the […]
GeoBlocking | What You Need to Know (+ how to beat it in 2026)
Geoblocking, also known as geo-restriction, is the act of completely blocking or limiting access to online content based on the physical location of the user. Geo-blocking is a common tactic used by international media streaming companies to protect licensing deals. Below I’d like to dive into a deeper explanation answering the questions what is geoblocking […]
DuckDuckGo vs Google | Private Search in 2026
Google tries hard to convince users that their search and internet data is secure; DuckDuckGo proudly points to their privacy policy that says they collect no data. Which is better? And what’s the difference when you compare DuckDuckGo vs Google in 2026? This is what we’re going to look at today. In the war of […]
How to Change Location on iPhone (2026 Tutorial)
Do you ever feel trapped by your iPhone’s location? When access to certain shows, apps, or geo-location-based games feel limited? In this tutorial, we’re going to explore exactly how you can change location on your iPhone to take back control of this personal data. Turns out it’s simpler than you’d think. From VPNs to Apple […]
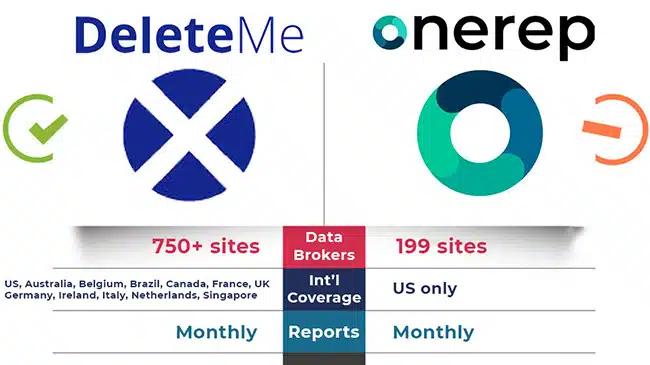
OneRep vs DeleteMe: Full 2026 Comparison for Data Privacy
Deciding between Onerep vs DeleteMe for your online privacy? This side-by-side comparison cuts through the noise to help you choose. We’ll explore how each service works to remove your personal information, discuss pricing, and touch on user experiences. Dive into the details without the fluff as we compare OneRep and DeleteMe to see which might […]